🔐 Information Security
Master of Information Technology (M.I.T.) - Second Semester
Subject Code: MIT122 - Information Security | Final Exam 2022
Full Marks: 60 | Pass Marks: 24 | Time: 3 Hours
Group A - Answer TWO Questions (2×12=24 Marks)
🔐 Question 1 12 Marks
Definition of Security Blueprint
A Security Blueprint is a comprehensive framework that serves as a detailed plan for designing, implementing, and managing an organization's information security program. It provides a structured approach to identifying security requirements, establishing controls, and creating a roadmap for protecting information assets. The blueprint acts as a architectural guide that aligns security initiatives with business objectives and risk management strategies.
Beneficiaries of Security Blueprint
- Organization/Enterprise: Gains a structured security posture, reduced risk exposure, regulatory compliance, and protection of critical assets
- IT Management: Receives clear guidelines for security implementation, resource allocation, and strategic planning
- Security Teams: Gets standardized procedures, defined roles, and measurable security metrics
- Employees: Benefits from clear security policies, awareness training, and safe working environment
- Customers/Clients: Enjoys protection of their data, privacy assurance, and trust in the organization's security practices
- Stakeholders/Investors: Gains confidence in the organization's risk management and governance practices
Services Provided by Security Blueprint
- Risk Assessment and Management: Identifies, analyzes, and prioritizes security risks; provides methodologies for risk treatment and mitigation strategies.
- Policy Development: Creates comprehensive security policies, standards, procedures, and guidelines that govern information security across the organization.
- Security Architecture Design: Defines the technical architecture including network security, application security, data protection mechanisms, and security infrastructure.
- Access Control Services: Establishes authentication, authorization, and accounting (AAA) frameworks; defines identity and access management (IAM) strategies.
- Incident Response Planning: Develops procedures for detecting, responding to, and recovering from security incidents including communication protocols and escalation paths.
- Business Continuity and Disaster Recovery: Ensures critical business functions continue during disruptions; provides backup and recovery strategies.
- Compliance Management: Maps security controls to regulatory requirements (GDPR, HIPAA, PCI-DSS, ISO 27001) and provides audit frameworks.
- Security Awareness and Training: Delivers educational programs to build security culture and reduce human-related security risks.
- Monitoring and Governance: Establishes security operations center (SOC) functions, continuous monitoring, and performance metrics.
- Vendor and Third-Party Risk Management: Provides frameworks for assessing and managing security risks from external partners and service providers.
🔑 Question 2 12 Marks
Secret-Key (Symmetric) Cryptography
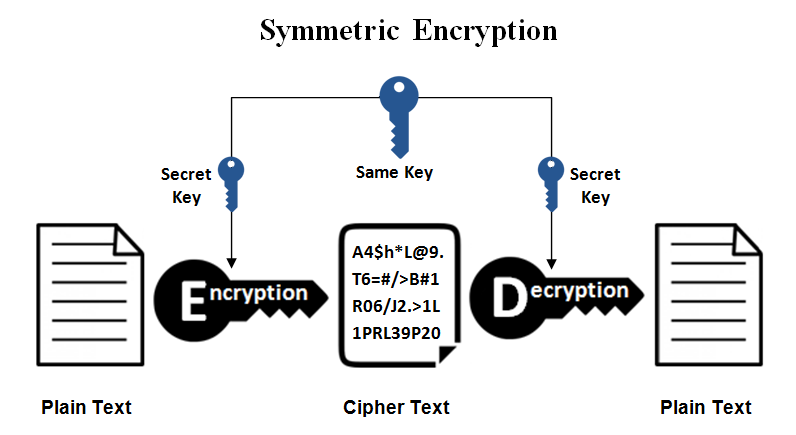
Advantages of Secret-Key Cryptography
- Speed and Efficiency: Symmetric algorithms are significantly faster than asymmetric algorithms, making them ideal for encrypting large amounts of data in real-time applications.
- Computational Efficiency: Requires less computational power and memory resources, suitable for devices with limited processing capabilities.
- Simplicity: Algorithms like AES, DES are mathematically simpler and easier to implement in hardware and software.
- Lower Latency: Minimal processing delay makes them suitable for high-speed communications and streaming data.
- Strong Security per Bit: Provides high security with relatively shorter key lengths compared to asymmetric cryptography.
- Widespread Standardization: Well-established standards (AES, 3DES) with extensive testing and validation.
Drawbacks of Secret-Key Cryptography
- Key Distribution Problem: The biggest challenge is securely sharing the secret key between communicating parties without interception.
- Scalability Issues: For n users to communicate securely, n(n-1)/2 keys are needed, creating massive key management overhead in large networks.
- No Non-repudiation: Since both parties share the same key, it's impossible to prove which party created a specific message.
- Key Compromise Risk: If the secret key is compromised, all past and future communications encrypted with that key are at risk.
- Lack of Authentication: Does not inherently provide sender authentication, as anyone with the key can create valid messages.
RSA Algorithm Explanation
RSA (Rivest-Shamir-Adleman) is an asymmetric cryptographic algorithm that uses a pair of keys: public key for encryption and private key for decryption. It is based on the mathematical difficulty of factoring large prime numbers.
RSA Key Generation Process:
- Select two large prime numbers: p and q
- Calculate n = p × q (modulus)
- Calculate Euler's totient function: φ(n) = (p-1) × (q-1)
- Choose public exponent e such that: 1 < e < φ(n) and gcd(e, φ(n))=1
- Calculate private exponent d such that: d × e ≡ 1 (mod φ(n))
- Public Key: (e, n) | Private Key: (d, n)
RSA Demonstration (Numerical Example)
Let p = 7, q = 11 (small primes for demonstration)
n = 7 × 11 = 77
φ(n) = (7-1) × (11-1) = 6 × 10 = 60
Choose e = 13 (gcd(13, 60) = 1)
Find d: d × 13 ≡ 1 (mod 60) → d = 37 (since 13×37=481, 481 mod 60 = 1)
Public Key: (13, 77) | Private Key: (37, 77)
Plaintext message M = 5 (where M < n)
Ciphertext C = M^e mod n = 5^13 mod 77
5^13 = 1,220,703,125
C = 1,220,703,125 mod 77 = 26
Ciphertext C = 26
Plaintext M = C^d mod n = 26^37 mod 77
Using modular exponentiation: 26^37 mod 77 = 5
Original message recovered: M = 5 ✓
RSA Applications
- Secure data transmission (SSL/TLS certificates)
- Digital signatures for authentication and non-repudiation
- Key exchange for symmetric encryption (hybrid systems)
- Secure email (PGP, S/MIME)
- VPN authentication and secure shell (SSH)
🛡️ Question 3 12 Marks
NSTISSC Security Model (McCumber Cube)
The NSTISSC (National Security Telecommunications and Information Systems Security Committee) security model, commonly known as the McCumber Cube, provides a comprehensive three-dimensional framework for information security. Developed by John McCumber in 1991, this model helps organizations understand and implement security across multiple dimensions.
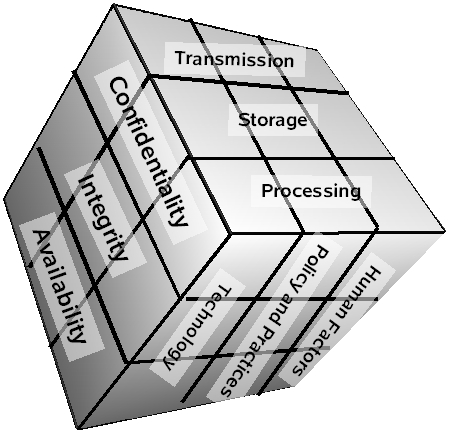
Three Dimensions of the McCumber Cube
| Dimension | Components | Description |
|---|---|---|
| X-Axis: Security Goals (CIA) | Confidentiality, Integrity, Availability | The foundational security objectives that must be maintained |
| Y-Axis: Information States | Storage, Transmission, Processing | The three states in which information can exist |
| Z-Axis: Security Measures | Technology, Policy & Practices, Human Factors | The categories of safeguards to protect information |
Detailed Components
Security Goals (X-Axis):
- Confidentiality: Ensuring information is accessible only to authorized individuals
- Integrity: Maintaining accuracy and completeness of information
- Availability: Ensuring timely and reliable access to information
Information States (Y-Axis):
- Storage: Data at rest (databases, files, backups)
- Transmission: Data in transit (networks, internet, wireless)
- Processing: Data being manipulated (CPU, memory operations)
Security Measures (Z-Axis):
- Technology: Hardware and software solutions (firewalls, encryption, IDS)
- Policy & Practices: Administrative controls, procedures, standards
- Human Factors: Training, awareness, personnel security
The model creates 27 cells (3×3×3), with each cell representing a specific security consideration. For example: "Confidentiality of Data in Storage through Technology" or "Integrity of Data in Processing through Human Factors."
Secure Software Development Life Cycle (Sec SDLC)
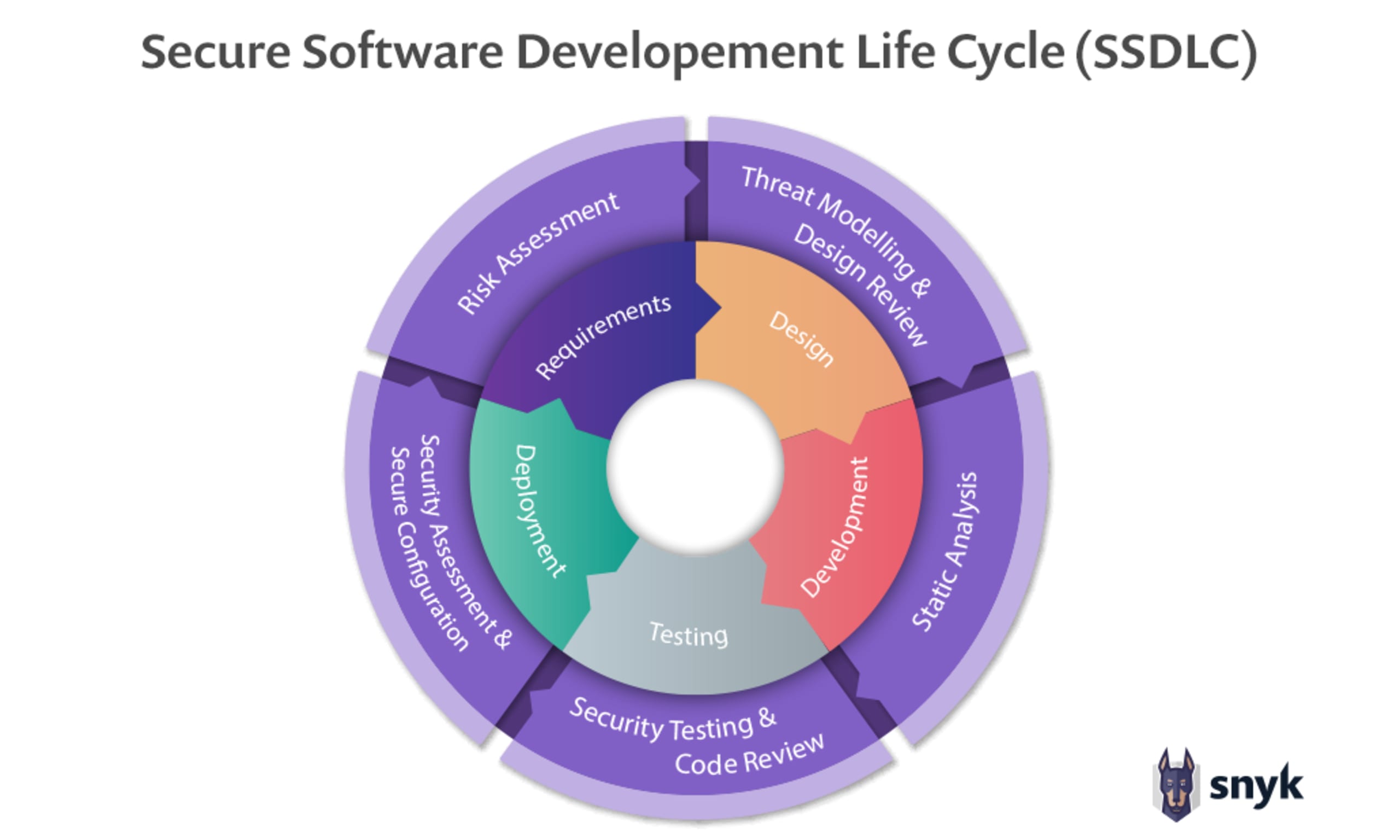
The Secure SDLC (Sec SDLC) integrates security activities into each phase of the traditional software development life cycle, ensuring security is built-in rather than bolted-on.
Phases of Sec SDLC
- Planning and Requirements Phase
- Identify security requirements and compliance needs
- Conduct risk assessment and threat modeling
- Define security metrics and acceptance criteria
- Establish security policies for the project
- Output: Security Requirements Specification (SRS)
- Design Phase
- Create secure architecture and design patterns
- Perform threat modeling (STRIDE, DREAD)
- Design security controls and countermeasures
- Plan for authentication, authorization, and audit mechanisms
- Output: Secure Design Document, Threat Model
- Development/Coding Phase
- Follow secure coding standards (OWASP, CERT)
- Implement input validation and output encoding
- Use secure libraries and frameworks
- Conduct peer code reviews with security focus
- Output: Secure Source Code
- Testing Phase
- Perform static application security testing (SAST)
- Conduct dynamic application security testing (DAST)
- Execute penetration testing
- Perform fuzz testing and vulnerability scanning
- Validate security requirements implementation
- Output: Security Test Reports, Vulnerability Assessment
- Deployment Phase
- Configure secure deployment environment
- Implement secure configuration management
- Set up monitoring and logging mechanisms
- Conduct final security verification
- Prepare incident response procedures
- Output: Secure Deployment Configuration
- Maintenance and Operations Phase
- Continuous security monitoring
- Patch management and vulnerability remediation
- Security incident response and management
- Regular security assessments and audits
- Security awareness training for operations team
- Output: Security Monitoring Reports, Patched System
- Disposal/Decommissioning Phase
- Secure data archiving or destruction
- Secure hardware disposal
- Documentation of system retirement
- Knowledge transfer and lessons learned
- Output: Decommissioning Certificate, Data Destruction Logs
- Reduces security vulnerabilities early when they are less costly to fix
- Decreases total cost of security ownership
- Ensures compliance with regulatory requirements
- Improves overall software quality and reliability
- Builds security awareness among development teams
Group B - Answer SIX Questions (6×6=36 Marks)
⚖️ Question 4 6 Marks
Computer Crime Definition
Computer crime (also known as cybercrime) refers to any illegal activity that involves a computer, network, or digital device as the target, tool, or place of criminal activity. The U.S. Department of Justice defines computer crime as "any violations of criminal law that involve a knowledge of computer technology for their perpetration, investigation, or prosecution."
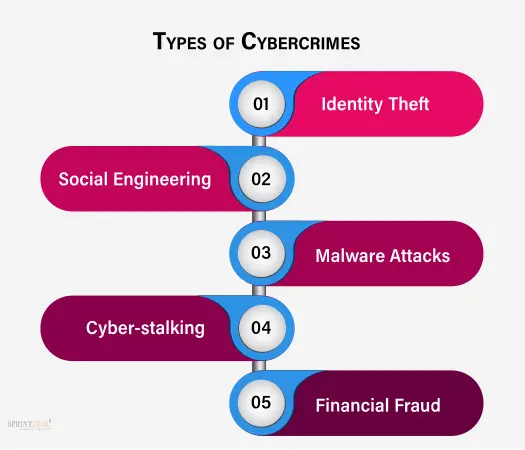
Categories of Computer Crime
- Crimes targeting computers: Viruses, malware, DDoS attacks, unauthorized access
- Crimes using computers: Fraud, identity theft, phishing, data theft
- Crimes where computer is incidental: Traditional crimes aided by computers (money laundering)
Ethics in Information Security
Information security ethics refers to the moral principles and standards that guide the behavior of security professionals in protecting information assets. It involves making responsible decisions about accessing, using, and protecting data while respecting privacy, confidentiality, and legal boundaries.
Prevailing Legal Issues
- Jurisdictional Challenges: Cybercrimes often cross international borders, creating complex jurisdictional issues. Determining which country's laws apply and securing international cooperation remains difficult.
- Evidence Collection and Admissibility: Digital evidence is fragile and easily altered. Courts require strict chain of custody procedures and forensic standards for evidence to be admissible.
- Privacy vs. Security Balance: Laws must balance individual privacy rights with national security needs. Controversies surround government surveillance, encryption backdoors, and data retention laws.
- Intellectual Property Protection: Digital piracy, software theft, and copyright infringement in cyberspace pose significant enforcement challenges.
- Data Protection Regulations: Compliance with GDPR (EU), CCPA (California), HIPAA (healthcare), and other data protection laws creates legal obligations for organizations.
- Liability Issues: Determining liability for security breaches involving third-party vendors, cloud providers, or software manufacturers remains legally complex.
Prevailing Ethical Issues
- Whistleblowing: Security professionals face ethical dilemmas when discovering illegal activities or severe vulnerabilities—whether to report internally or go public.
- Responsible Disclosure: Ethical debate over how and when to disclose security vulnerabilities to vendors and the public to maximize protection while minimizing harm.
- Privacy in the Digital Age: Ethical questions about monitoring employee communications, customer tracking, and the extent of surveillance justified for security.
- Artificial Intelligence and Automation: Ethical concerns about AI in security—algorithmic bias, autonomous decision-making in cyber defense, and accountability for AI actions.
- Hacktivism: Ethical debates about hacking for political or social causes—whether it's civil disobedience or criminal activity.
- Dual-Use Research: Ethical challenges when security research that could improve defenses could also be used to create better attacks.
- Professional Responsibility: Security professionals must navigate conflicts between employer interests, professional standards, and public safety.
🔒 Question 5 6 Marks
Intrusion Detection System (IDS)
An Intrusion Detection System (IDS) is a security technology that monitors network traffic or system activities for malicious activities or policy violations. It operates as a passive monitoring system that detects and alerts administrators about potential security threats but does not take automatic action to block them.
Types of IDS:
- Network-based IDS (NIDS): Monitors network traffic at strategic points analyzing packets for suspicious patterns
- Host-based IDS (HIDS): Monitors individual hosts/servers for internal threats, file integrity, and system calls
- Signature-based IDS: Detects known threats by matching traffic against a database of attack signatures
- Anomaly-based IDS: Establishes baseline behavior and alerts on deviations from normal patterns
Intrusion Prevention System (IPS)
An Intrusion Prevention System (IPS) is an active security system that not only detects threats like an IDS but also takes automated actions to prevent them. It sits inline with network traffic and can block malicious activities in real-time.
IPS Actions:
- Dropping malicious packets
- Blocking source IP addresses
- Resetting connections
- Alerting administrators
- Reconfiguring firewalls to block traffic

Differences between IDS/IPS and Firewall
| Aspect | Firewall | IDS | IPS |
|---|---|---|---|
| Primary Function | Access control based on rules | Detection and alerting | Detection and prevention |
| Placement | Network perimeter/boundaries | Passive (out of band) | Inline (in the traffic path) |
| Action | Allow/Deny based on policy | Alert only (passive) | Block/Prevent (active) |
| Inspection Level | Packet headers, ports, protocols | Deep packet inspection | Deep packet inspection |
| Threat Type | External threats, unauthorized access | Known and unknown attacks | Known and unknown attacks |
| Response Time | Real-time blocking | Detection with delay (logging) | Real-time prevention |
| False Positive Impact | Blocked legitimate traffic | Alert fatigue | Blocked legitimate traffic |
| Deployment Complexity | Low to Medium | Medium | High (inline deployment risks) |
Key Differences Explained
- Functionality: Firewalls act as gatekeepers using predefined rules (IP addresses, ports), while IDS/IPS analyze content for malicious patterns. Firewalls block based on "who" and "where," IDS/IPS detect "what" is happening.
- Positioning: Firewalls are deployed at network boundaries. IDS is passive (monitoring a copy of traffic), while IPS is inline (traffic flows through it).
- Depth of Inspection: Traditional firewalls examine headers; modern Next-Gen Firewalls (NGFW) include deep inspection. IDS/IPS inherently perform deep packet inspection analyzing payload content.
- Response Capability: Firewalls enforce policy decisions; IDS only observes and reports; IPS actively intervenes to stop threats.
- Attack Detection: Firewalls cannot detect attacks within allowed traffic (e.g., SQL injection over HTTP port 80). IDS/IPS can detect application-layer attacks regardless of port.
Complementary Relationship: These technologies work together—firewalls provide perimeter defense, IDS provides visibility and logging, and IPS provides active threat prevention. Modern solutions often combine these into Unified Threat Management (UTM) or Next-Generation Firewall (NGFW) platforms.
📜 Question 6 6 Marks
Laws in Information Security
1. Computer Fraud and Abuse Act (CFAA) - USA
Enacted in 1986, the CFAA is the primary U.S. federal anti-hacking law. It criminalizes unauthorized access to computer systems, exceeding authorized access, and damaging protected computers. It covers activities including malware distribution, denial of service attacks, and trafficking in passwords.
2. General Data Protection Regulation (GDPR) - EU
Implemented in 2018, GDPR is the world's strongest data protection law. It grants EU citizens rights over their personal data including right to access, right to be forgotten, and data portability. Organizations face fines up to 4% of global revenue for non-compliance.
3. Health Insurance Portability and Accountability Act (HIPAA) - USA
HIPAA establishes standards for protecting sensitive patient health information. It requires healthcare organizations to implement administrative, physical, and technical safeguards to ensure confidentiality, integrity, and availability of electronic protected health information (ePHI).
4. Sarbanes-Oxley Act (SOX) - USA
Enacted in 2002 following corporate scandals, SOX mandates strict financial record-keeping and reporting for public companies. It requires CEOs and CFOs to personally certify financial reports and establishes internal control requirements for financial data.
5. Information Technology Act 2000 - India
India's primary cyber law that provides legal recognition to electronic transactions, defines cybercrimes (hacking, data theft, identity theft), and establishes penalties. The 2008 amendment added provisions for data protection and intermediary liability.
6. Payment Card Industry Data Security Standard (PCI DSS)
While not a government law, PCI DSS is a contractual requirement for any organization handling credit card data. It mandates security controls including encryption, access control, network monitoring, and regular security testing.
Ethics in Information Security
1. Professional Codes of Ethics
- (ISC)² Code of Ethics: Requires certified professionals to protect society, the common good, and the infrastructure; act honorably and honestly; and provide diligent service.
- ISACA Code of Professional Ethics: Emphasizes honesty, objectivity, due diligence, and confidentiality in information systems auditing and control.
- EC-Council Code of Ethics: Guides ethical hackers to respect privacy, obtain proper authorization, and disclose vulnerabilities responsibly.
2. Key Ethical Principles
- Confidentiality: Respecting the privacy of information and not disclosing sensitive data improperly
- Integrity: Maintaining honesty and strong moral principles; not engaging in deceptive practices
- Professional Competence: Maintaining skills and knowledge; only performing services within one's competence
- Public Interest: Prioritizing public safety and welfare over personal or organizational gain
- Responsible Disclosure: Ethically reporting vulnerabilities to allow organizations to fix them before public disclosure
Risk Control Strategies

1. Risk Avoidance
Eliminating the risk by discontinuing the activity that creates it. This is the most effective but often least practical strategy.
- Example: Not storing sensitive customer data to avoid data breach risk
- Example: Discontinuing use of outdated, unsupported software
- Example: Avoiding business in high-risk geographic regions
2. Risk Mitigation (Reduction)
Implementing controls to reduce the likelihood or impact of a risk. This is the most common strategy.
- Technical controls: Firewalls, encryption, antivirus, intrusion detection systems
- Administrative controls: Policies, procedures, security awareness training
- Physical controls: Locks, guards, surveillance, access cards
- Example: Implementing multi-factor authentication to reduce account compromise risk
3. Risk Transference (Sharing)
Shifting the financial impact of risk to a third party.
- Insurance: Cyber liability insurance transfers financial risk to insurers
- Outsourcing: Transferring risk to specialized vendors (cloud providers, security firms)
- Contracts: Service Level Agreements (SLAs) and liability clauses
- Derivatives: Cyber risk insurance-linked securities for large organizations
4. Risk Acceptance
Consciously deciding to accept the risk without implementing controls, typically when the cost of control exceeds the potential loss.
- Informed acceptance: Management understands and formally accepts the risk
- Residual acceptance: Accepting remaining risk after mitigation efforts
- Requires documentation and management approval
- Usually for low-impact, low-probability risks
5. Risk Monitoring and Review
Continuous process of tracking identified risks, monitoring residual risks, and identifying new risks.
- Regular risk assessments and vulnerability scans
- Key Risk Indicators (KRIs) monitoring
- Incident tracking and analysis
- Control effectiveness testing
⚠️ Question 7 6 Marks
Emerging Threats to Information Security

1. AI-Powered Cyber Attacks
Artificial Intelligence and Machine Learning are being weaponized by cybercriminals to create sophisticated, adaptive attacks that evade traditional security defenses.
- Deepfake Technology: Creating realistic audio/video for social engineering and CEO fraud
- AI-Generated Phishing: Highly personalized spear-phishing emails that mimic writing styles
- Automated Vulnerability Discovery: AI systems scanning for and exploiting vulnerabilities faster than human defenders
- Adaptive Malware: Malware that changes its signature to evade detection using machine learning
- Password Cracking: Neural networks trained to predict passwords more efficiently
2. Ransomware and Ransomware-as-a-Service (RaaS)
Ransomware has evolved from simple file encryption to sophisticated extortion operations, with RaaS lowering the barrier to entry for cybercriminals.
- Double Extortion: Encrypting data AND threatening to leak stolen data
- Triple Extortion: Adding DDoS attacks and targeting customers/vendors
- Supply Chain Ransomware: Targeting MSPs and software vendors to affect multiple organizations
- Critical Infrastructure Targeting: Attacking hospitals, utilities, and government services
- Zero-Day Exploits: Using previously unknown vulnerabilities before patches are available
3. Cloud Security Threats
As organizations rapidly migrate to cloud environments, misconfigurations and cloud-specific vulnerabilities create new attack surfaces.
- Misconfigured Storage: Publicly exposed S3 buckets, Azure blobs containing sensitive data
- Insecure APIs: Poorly secured cloud service APIs allowing unauthorized access
- Cloud Jacking: Compromising cloud accounts through credential theft or session hijacking
- Insider Threats: Malicious administrators or compromised insider credentials in multi-tenant environments
- Denial of Service: Cloud resource exhaustion attacks causing service unavailability
4. Internet of Things (IoT) and OT Threats
The proliferation of connected devices and convergence of IT and Operational Technology (OT) creates unprecedented attack surfaces.
- Botnet Recruitment: Insecure IoT devices recruited into massive botnets (Mirai, Mozi)
- Industrial Control System Attacks: Targeting SCADA, PLC systems in critical infrastructure
- Medical Device Hacking: Compromising pacemakers, insulin pumps, and hospital equipment
- Smart Home Invasion: Using IoT devices as entry points to home and corporate networks
- Shadow IoT: Unauthorized devices connecting to corporate networks without IT knowledge
5. Supply Chain Attacks
Attackers target less-secure elements in the supply chain—software vendors, hardware manufacturers, or service providers—to compromise multiple downstream organizations.
- Software Supply Chain: Injecting malware into legitimate software updates (SolarWinds, Kaseya)
- Hardware Compromise: Tampering with devices during manufacturing or shipping
- Third-Party Compromise: Breaching vendors with access to target networks
- Open Source Poisoning: Compromising popular open-source libraries and repositories
- Dependency Confusion: Uploading malicious packages to public repositories with names similar to internal packages
Additional Emerging Threats
- Quantum Computing Threats: Future quantum computers threatening current encryption standards
- 5G Network Vulnerabilities: New attack surfaces in 5G infrastructure and edge computing
- Cryptocurrency and Blockchain Attacks: Smart contract vulnerabilities, wallet theft, and DeFi exploits
- Fileless Malware: Memory-resident attacks leaving no traditional file signatures
🌐 Question 8 6 Marks
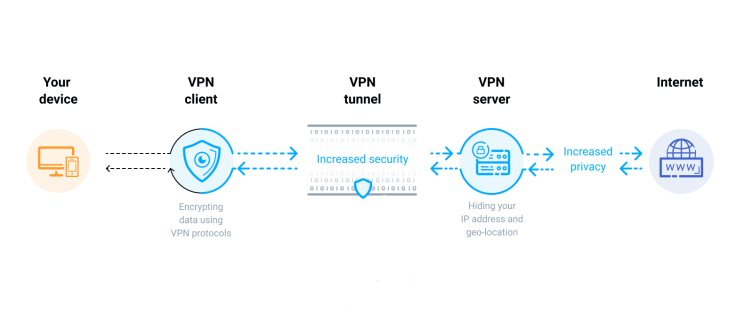
Virtual Private Network (VPN) Definition
A Virtual Private Network (VPN) is a technology that creates a secure, encrypted connection (tunnel) over a less secure network, typically the public internet. It extends a private network across a public network, enabling users to send and receive data as if their devices were directly connected to the private network, while benefiting from the functionality, security, and management policies of that private network.
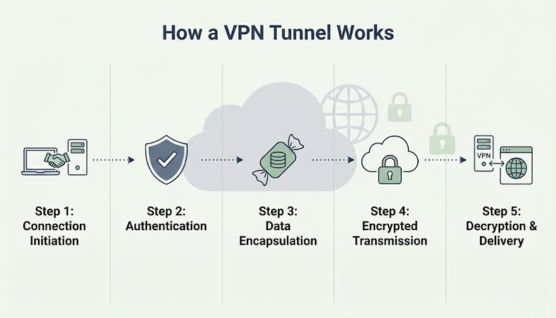
How VPN Works
1. Tunneling Process
VPN uses tunneling protocols to encapsulate data packets within another packet before sending them through the tunnel. This hides the original data and its destination from outsiders.
- Connection Establishment: User initiates VPN connection to VPN server using VPN client software
- Authentication: User credentials or certificates are verified (username/password, digital certificates, or multi-factor authentication)
- Tunnel Creation: VPN client and server negotiate encryption protocols and establish a secure tunnel
- Encryption: Data from the user's device is encrypted using algorithms like AES-256
- Encapsulation: Encrypted data is wrapped in a new packet with VPN server as destination
- Transmission: Data travels through the internet to VPN server
- Decryption: VPN server decrypts the data and sends it to the intended destination
- Return Path: Response follows the reverse path, encrypted by server and decrypted by client
2. VPN Protocols
| Protocol | Description | Use Case |
|---|---|---|
| OpenVPN | Open-source, highly configurable, uses SSL/TLS encryption | Most secure, widely used |
| IPsec/IKEv2 | Internet Protocol Security with Internet Key Exchange | Mobile devices, fast reconnection |
| WireGuard | Modern, lightweight, fast cryptographic protocol | High performance, newer standard |
| L2TP/IPsec | Layer 2 Tunneling Protocol with IPsec encryption | Native OS support |
| PPTP | Point-to-Point Tunneling Protocol (older, less secure) | Legacy systems (not recommended) |
3. Types of VPN
- Remote Access VPN: Individual users connect to corporate network from remote locations
- Site-to-Site VPN: Connects entire networks (e.g., branch offices to headquarters)
- Client-to-Site VPN: Similar to remote access but typically for consumer VPN services
- SSL VPN: Browser-based access without dedicated client software
Benefits of Using VPNs
1. Enhanced Security and Privacy
- Data Encryption: Protects data from interception by encrypting all traffic, preventing ISPs, hackers, or government agencies from reading content
- IP Address Masking: Hides user's real IP address, making tracking and profiling difficult
- Protection on Public Wi-Fi: Secures connections on unsecured public networks (cafes, airports, hotels) preventing man-in-the-middle attacks
- DNS Leak Protection: Prevents DNS queries from revealing browsing history
2. Remote Access and Business Continuity
- Enables secure work-from-home arrangements
- Provides access to internal corporate resources (file servers, intranets, applications)
- Maintains business operations during travel or emergencies
- Reduces need for expensive dedicated leased lines
3. Bypassing Censorship and Geo-Restrictions
- Access content blocked by geographic restrictions (streaming services)
- Bypass government censorship in restrictive regions
- Access global business resources regardless of location
- Avoid price discrimination based on location
4. Cost Savings
- Eliminates expensive dedicated WAN links between offices
- Reduces long-distance telephone charges using VoIP
- Allows use of cheaper internet connections instead of private lines
- Lowers travel costs through remote access capabilities
5. Regulatory Compliance
- Helps meet data protection requirements (GDPR, HIPAA) when transmitting sensitive data
- Provides encrypted channels for financial transactions
- Creates audit trails for compliance reporting
- Protects intellectual property during transmission
6. Network Scalability
- Easily add new users without significant infrastructure changes
- Accommodate growing remote workforce
- Connect new branch offices quickly
- Flexible bandwidth allocation
🏗️ Question 9 6 Marks
Information Security Implementation
Implementing information security is a comprehensive process that requires a systematic approach integrating both technical controls and non-technical (administrative/physical) measures. Successful implementation follows a structured methodology based on risk assessment and defense-in-depth principles.
Implementation Process
Phase 1: Planning and Assessment
- Conduct comprehensive risk assessment identifying assets, threats, and vulnerabilities
- Define security objectives aligned with business goals
- Establish security governance structure and roles
- Develop security policies, standards, and procedures
- Create implementation roadmap with priorities and timelines
- Allocate budget and resources
Phase 2: Design and Architecture
- Design secure network architecture with segmentation
- Plan identity and access management (IAM) framework
- Select appropriate security technologies and tools
- Design incident response and business continuity plans
- Establish security monitoring and logging infrastructure
Phase 3: Deployment and Integration
- Implement technical controls in phases (pilot then production)
- Deploy administrative controls and procedures
- Establish physical security measures
- Configure and tune security tools
- Integrate security into business processes
Phase 4: Testing and Validation
- Conduct vulnerability assessments and penetration testing
- Test incident response procedures
- Validate backup and recovery processes
- Perform security awareness validation
- Audit compliance with policies
Phase 5: Operations and Maintenance
- Continuous monitoring and threat detection
- Regular patching and updates
- Security awareness training and updates
- Periodic reassessment and improvement
- Incident response and lessons learned integration
Technical Aspects of Implementation
1. Network Security Controls
- Firewalls: Next-generation firewalls (NGFW) with deep packet inspection, application control, and intrusion prevention
- Network Segmentation: VLANs, subnets, and micro-segmentation to isolate critical systems
- VPN Solutions: Remote access and site-to-site VPNs for secure connectivity
- Intrusion Detection/Prevention Systems (IDS/IPS): Real-time threat detection and blocking
- Network Access Control (NAC): Device authentication and compliance checking before network access
2. Endpoint Security
- Antivirus/Antimalware: Endpoint protection platforms (EPP) with behavioral analysis
- Endpoint Detection and Response (EDR): Advanced threat detection and incident investigation
- Host-based Firewalls: Individual device protection
- Disk Encryption: Full disk encryption (BitLocker, FileVault) for data at rest
- Mobile Device Management (MDM): Security for smartphones and tablets
3. Identity and Access Management (IAM)
- Authentication: Multi-factor authentication (MFA), biometrics, smart cards
- Single Sign-On (SSO): Centralized authentication reducing password fatigue
- Privileged Access Management (PAM): Securing administrative accounts
- Role-Based Access Control (RBAC): Access based on job functions
- Identity Governance: Automated provisioning and access reviews
4. Data Protection
- Encryption: Data at rest (AES-256), data in transit (TLS 1.3), and data in use
- Data Loss Prevention (DLP): Preventing unauthorized data exfiltration
- Database Security: Activity monitoring, encryption, and access controls
- Backup Solutions: Encrypted, immutable backups with regular testing
5. Security Monitoring and Operations
- Security Information and Event Management (SIEM): Centralized log collection and analysis
- Security Orchestration, Automation and Response (SOAR): Automated incident response
- Threat Intelligence Platforms: Integration of external threat data
- Vulnerability Management: Continuous scanning and patch management
Non-Technical Aspects of Implementation
1. Governance and Management
- Security Policies: Acceptable use, password, remote access, and data classification policies
- Security Governance Structure: CISO role, security committees, and reporting lines
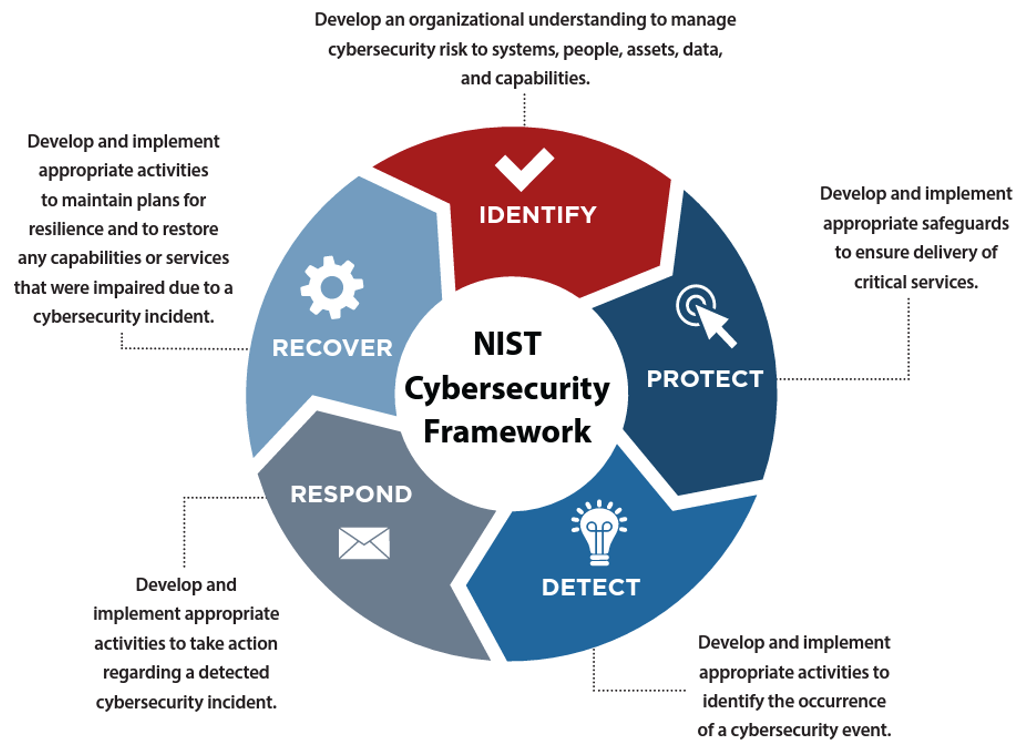
- Risk Management Framework: ISO 27001, NIST CSF, or COBIT adoption
- Third-Party Risk Management: Vendor assessment and monitoring programs
- Compliance Management: GDPR, HIPAA, PCI-DSS, SOX compliance programs
2. Human Resources Security
- Background Checks: Pre-employment screening for sensitive positions
- Security Awareness Training: Regular training on phishing, social engineering, and safe practices
- Role-Based Training: Specialized training for developers, administrators, and executives
- Simulated Exercises: Phishing simulations and tabletop exercises
- Clear Termination Procedures: Immediate revocation of access upon departure
3. Physical Security
- Access Control: Key cards, biometric readers, and visitor management
- Surveillance: CCTV monitoring of critical areas
- Environmental Controls: Fire suppression, climate control, and power backup
- Secure Disposal: Shredding documents and degaussing/destroying storage media
- Workspace Security: Clean desk policies and screen privacy filters
4. Administrative Procedures
- Change Management: Controlled process for system changes with security review
- Incident Response Plan: Documented procedures for security breaches
- Business Continuity/Disaster Recovery: Plans for maintaining operations during disruptions
- Asset Management: Inventory and classification of information assets
- Secure Development Lifecycle: Security integration in software development
5. Legal and Compliance
- Contracts and Agreements: Security requirements in vendor contracts and employment agreements
- Intellectual Property Protection: NDAs and IP handling procedures
- Privacy Program: Privacy impact assessments and data subject rights management
- Audit and Assessment: Regular internal and external security audits
Integration of Technical and Non-Technical Aspects
Effective security implementation requires seamless integration:
- Technical controls must be supported by policies (e.g., encryption technology backed by data classification policy)
- Security awareness training explains how to use technical controls properly
- Physical security complements logical access controls
- Incident response plans define how to use technical monitoring tools
- Governance ensures technical investments align with business risk
Success depends on viewing information security as a continuous process involving people, processes, and technology working together in a layered defense strategy.
📝 Question 10 6 Marks
Following are detailed notes on all three topics. Students should answer any TWO as per the question.
(a) Risk Assessment
Risk Assessment is the systematic process of identifying, analyzing, and evaluating risks to organizational operations, assets, and individuals. It forms the foundation of an effective information security management program by helping organizations understand their threat landscape and prioritize security investments.
Components of Risk Assessment
- Risk Identification
- Inventory of information assets (hardware, software, data, personnel)
- Identification of threats (natural, human, environmental)
- Identification of vulnerabilities (weaknesses that threats can exploit)
- Documentation of existing controls
- Risk Analysis
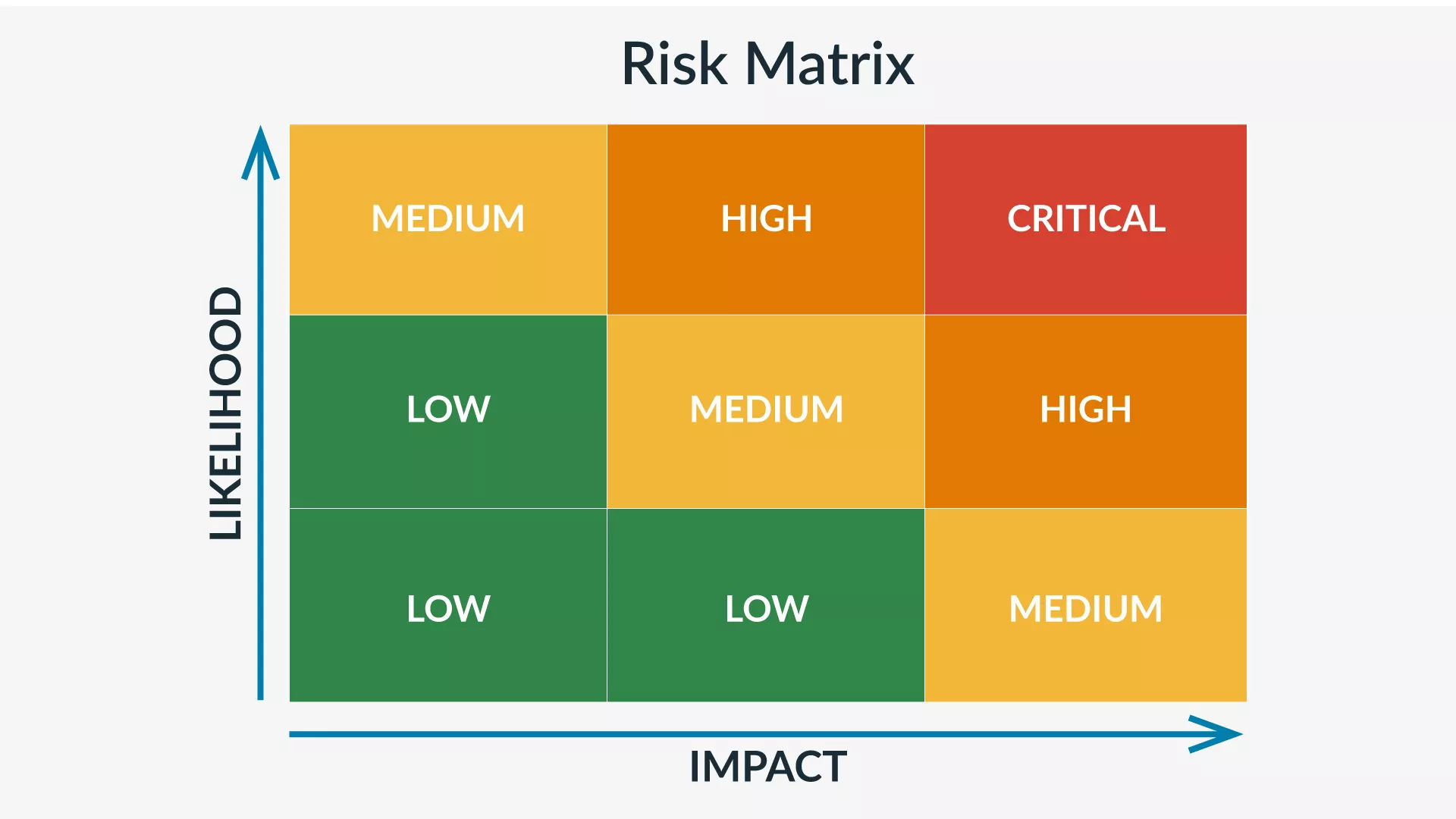
- Qualitative Analysis: Uses subjective ratings (High/Medium/Low) based on expert judgment
- Quantitative Analysis: Assigns numerical values (Annualized Loss Expectancy, Single Loss Expectancy)
- Determination of likelihood (probability of occurrence)
- Assessment of impact (financial, reputational, operational)
- Risk Evaluation
- Comparing identified risks against risk criteria
- Prioritizing risks based on severity
- Determining risk treatment options (accept, mitigate, transfer, avoid)
- Aligning with organizational risk appetite
Risk Assessment Methodologies
| Methodology | Description | Best For |
|---|---|---|
| ISO 27005 | International standard for information security risk management | Organizations seeking certification |
| NIST SP 800-30 | U.S. government risk assessment guideline | Federal agencies and contractors |
| OCTAVE | Operationally Critical Threat, Asset, and Vulnerability Evaluation | Self-directed assessments |
| FAIR | Factor Analysis of Information Risk (quantitative) | Financial risk quantification |
Key Formulas in Quantitative Risk Assessment
Annualized Rate of Occurrence (ARO) = Expected frequency per year
Annualized Loss Expectancy (ALE) = SLE × ARO
Risk Value = Likelihood × Impact
Benefits of Risk Assessment
- Informed decision-making for security investments
- Regulatory compliance demonstration
- Prioritization of security efforts
- Reduced unexpected security incidents
- Improved communication with stakeholders
- Basis for business continuity planning
(b) Digital Forensics
Digital Forensics (also known as computer forensics or cyber forensics) is the scientific process of identifying, preserving, analyzing, and presenting digital evidence in a manner that is legally acceptable. It involves the investigation of computer systems, networks, and digital storage media to uncover evidence of cybercrimes, policy violations, or unauthorized activities.
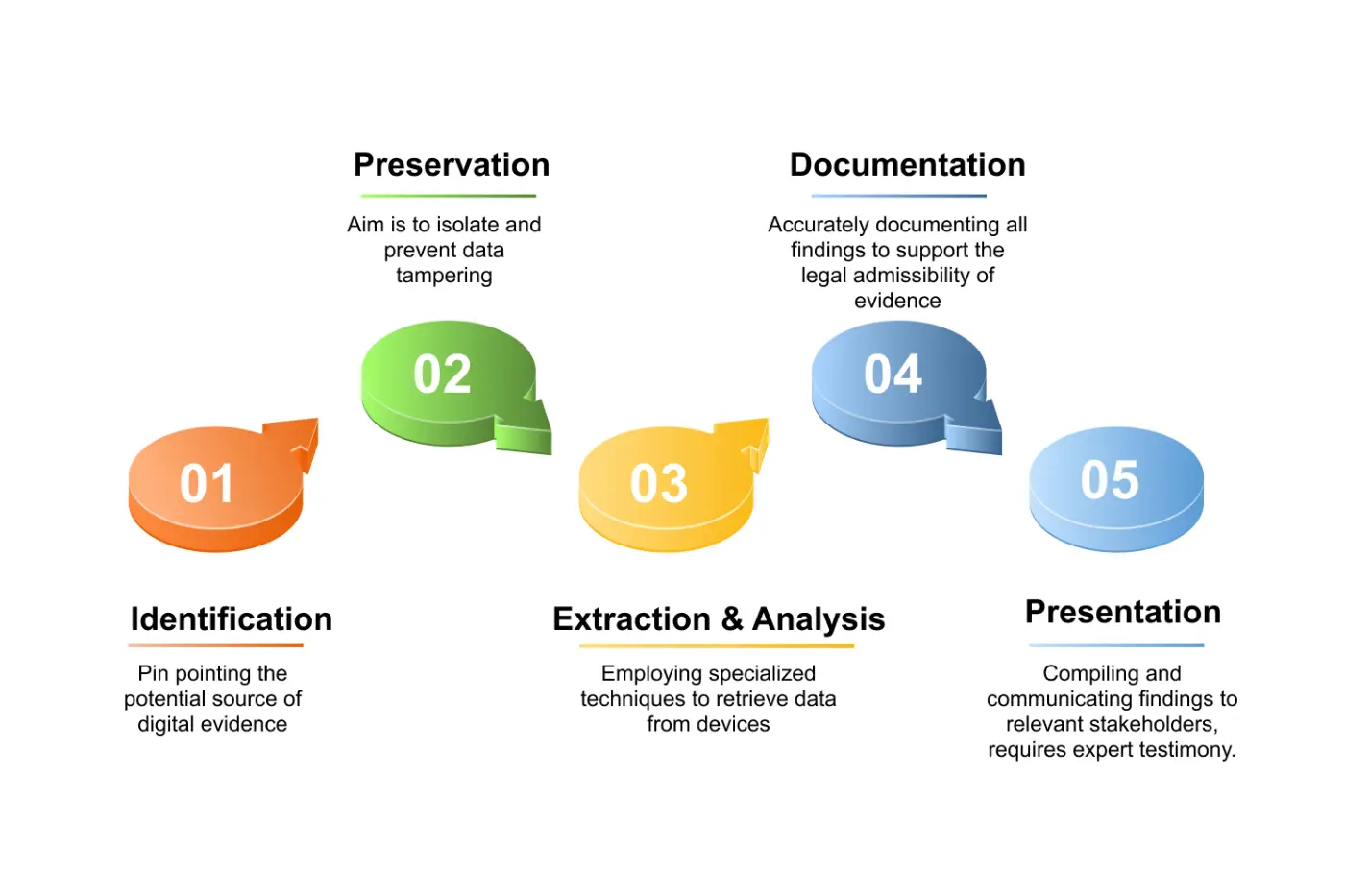
Phases of Digital Forensics
- Identification
- Recognizing potential evidence sources (computers, mobile devices, cloud storage, IoT devices)
- Determining the scope of investigation
- Identifying relevant legal and policy issues
- Securing the incident scene to prevent evidence contamination
- Preservation (Collection)
- Creating forensic images (bit-by-bit copies) of storage media
- Maintaining chain of custody documentation
- Using write blockers to prevent modification of original evidence
- Photographing and documenting the physical scene
- Hashing (MD5, SHA-256) to verify evidence integrity
- Extraction and Analysis
- Recovering deleted files and data fragments
- Examining file metadata, timestamps, and system logs
- Analyzing network traffic and communication records
- Decrypting encrypted data when possible
- Using forensic tools (EnCase, FTK, Autopsy, Sleuth Kit)
- Timeline reconstruction of events
- Documentation
- Detailed recording of all procedures and findings
- Maintaining logs of all tools used and their versions
- Documenting the chain of custody throughout
- Creating comprehensive reports of investigative steps
- Presentation
- Preparing clear, understandable reports for legal proceedings
- Presenting technical findings to non-technical audiences
- Providing expert testimony in court
- Ensuring evidence admissibility standards are met
Types of Digital Forensics
| Type | Focus Area | Key Activities |
|---|---|---|
| Computer Forensics | Desktop/laptop systems | Hard drive analysis, file recovery |
| Network Forensics | Network traffic and logs | Packet capture, flow analysis |
| Mobile Forensics | Smartphones and tablets | App data, call logs, GPS data |
| Cloud Forensics | Cloud storage and services | Multi-tenant data acquisition |
| Memory Forensics | RAM and volatile data | Running processes, encryption keys |
| Database Forensics | Database systems | Transaction logs, schema analysis |
Legal and Ethical Considerations
- Admissibility: Evidence must meet legal standards (authentic, reliable, best evidence)
- Privacy: Balancing investigation needs with privacy rights
- Chain of Custody: Unbroken documentation of evidence handling
- Authorization: Proper legal authority (warrants, consent, policy authority)
- Professional Standards: Following ethical guidelines of professional forensic organizations
Common Forensic Tools
- Commercial: EnCase, Forensic Toolkit (FTK), Cellebrite (mobile), Oxygen Forensic Suite
- Open Source: Autopsy, Sleuth Kit, Volatility (memory), Wireshark (network)
- Specialized: X-Ways Forensics, SANS SIFT, Paladin (Linux forensic suite)
(c) The SDLC (Software Development Life Cycle)
The Software Development Life Cycle (SDLC) is a structured methodology that defines the process used by organizations to design, develop, test, and deploy high-quality software. It provides a systematic approach to software development ensuring that the final product meets customer requirements, is completed on time and within budget, and maintains quality standards.

Phases of SDLC
- Planning and Requirement Analysis
- Feasibility study (technical, operational, economic, schedule)
- Gathering business requirements from stakeholders
- Resource allocation and project scheduling
- Risk identification and mitigation planning
- Output: Project Plan, Feasibility Report, Requirements Document
- System Design
- High-level design (HLD): Architecture, system components, interfaces
- Low-level design (LLD): Detailed module specifications, database design
- UI/UX design and prototyping
- Technology stack selection
- Output: Design Document, Architecture Diagrams, Data Models
- Implementation (Coding)
- Writing code according to design specifications
- Following coding standards and best practices
- Version control and configuration management
- Code reviews and pair programming
- Output: Source Code, Unit Test Results, Technical Documentation
- Testing
- Unit testing (individual components)
- Integration testing (combined modules)
- System testing (complete application)
- User Acceptance Testing (UAT) by stakeholders
- Performance, security, and compatibility testing
- Output: Test Plans, Test Cases, Bug Reports, Test Summary
- Deployment
- Release planning and environment preparation
- Data migration and system configuration
- User training and documentation handover
- Phased rollout (pilot, production)
- Output: Deployed System, User Manuals, Training Materials
- Maintenance
- Corrective maintenance (bug fixes)
- Adaptive maintenance (changes for new environments)
- Perfective maintenance (performance improvements, new features)
- Preventive maintenance (avoiding future problems)
- Output: Patches, Updates, Release Notes
SDLC Models
| Model | Approach | Best For |
|---|---|---|
| Waterfall | Sequential, linear approach | Clear requirements, stable projects |
| Agile | Iterative, incremental development | Changing requirements, customer collaboration |
| Spiral | Risk-driven iterative model | Large, complex, high-risk projects |
| V-Model | Verification and validation parallel | Projects requiring strict validation |
| DevOps | Development and operations integration | Continuous deployment environments |
Importance of SDLC
- Quality Assurance: Systematic testing ensures fewer defects in production
- Cost Control: Early defect detection reduces costly fixes later
- Project Management: Clear milestones and deliverables for tracking progress
- Risk Management: Structured approach identifies and mitigates risks early
- Stakeholder Communication: Defined phases improve communication with clients and teams
- Documentation: Comprehensive records support maintenance and future development
- Reproducibility: Standardized process enables consistent results across projects
SDLC vs Secure SDLC (SSDLC)
While traditional SDLC focuses on functional requirements, Secure SDLC (SSDLC) integrates security activities throughout each phase—threat modeling in design, secure coding in implementation, security testing in validation, and vulnerability management in maintenance. This "shift-left" approach ensures security is built-in rather than added as an afterthought.