🛡️ Information Security
Master of Information Technology (M.I.T.) - Second Semester
Final Exam 2024 | Subject Code: MIT122
Group A - Answer TWO Questions (2×12=24 Marks)
🔄 Question 1 6+6 Marks
🔄 Role of Security SDLC (SSDLC) in Creating Secure Software Applications
Security Software Development Life Cycle (SSDLC) integrates security practices into every phase of traditional SDLC. Unlike conventional development where security is an afterthought, SSDLC adopts a "shift-left" approach embedding security from the initial planning stage.
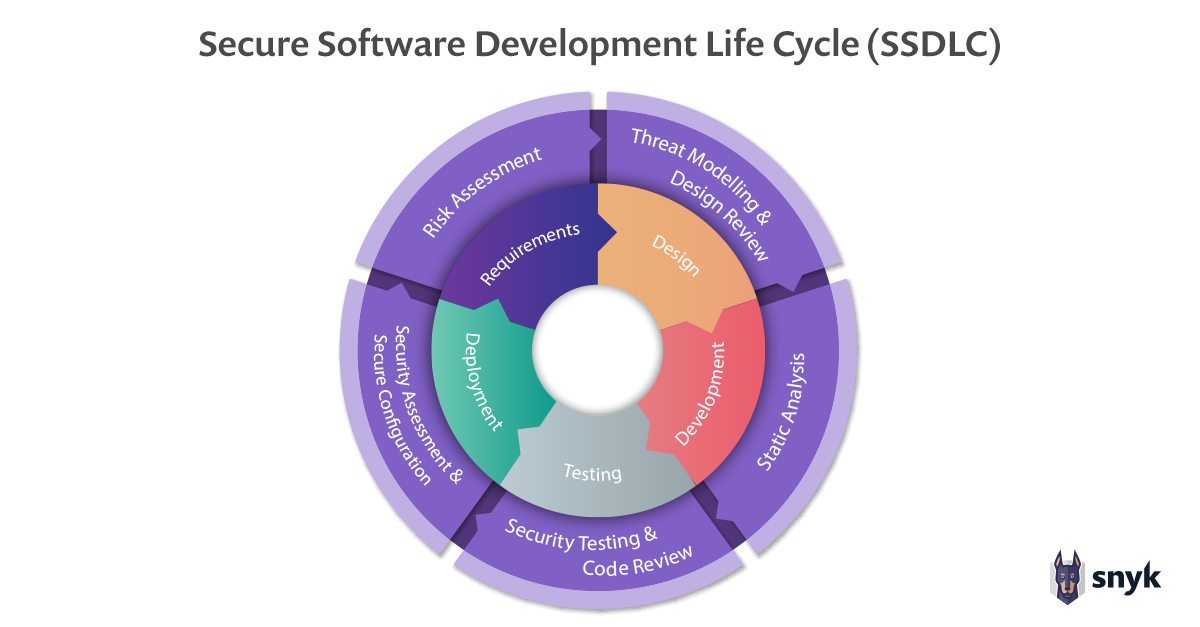
Key Phases and Security Integration:
- Planning & Requirements: Security requirements gathering, threat modeling, compliance mapping (GDPR, ISO 27001), and risk assessment
- Design: Secure architecture design, attack surface analysis, secure design patterns implementation
- Development: Secure coding standards (OWASP, CERT), static application security testing (SAST), code reviews
- Testing: Dynamic application security testing (DAST), penetration testing, vulnerability scanning
- Deployment: Secure configuration management, environment hardening, secrets management
- Maintenance: Continuous monitoring, patch management, incident response planning
Benefits of SSDLC:
- Reduces cost of fixing vulnerabilities (100x cheaper to fix in design vs production)
- Ensures compliance with regulatory requirements
- Builds customer trust and brand reputation
- Prevents data breaches and associated financial losses
🚀 How Businesses Ensure Secure Development Operations (DevSecOps)
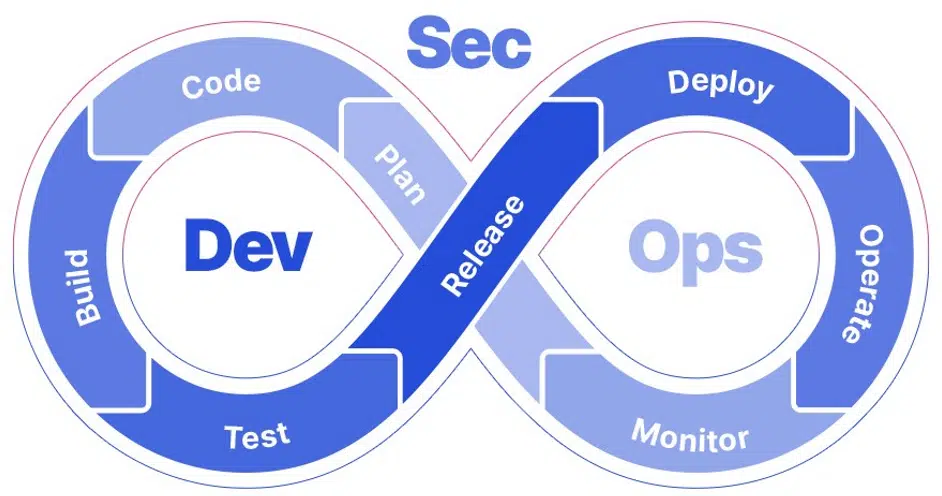
Organizations implement DevSecOps to automate security integration:
- Automated Security Testing: Integrate SAST, DAST, and dependency scanning into CI/CD pipelines
- Infrastructure as Code (IaC): Security policies defined as code ensuring consistent secure deployments
- Container Security: Image scanning, runtime protection, and orchestration security (Kubernetes policies)
- Secrets Management: Tools like HashiCorp Vault, AWS Secrets Manager for credential protection
- Security Champions Program: Training developers in secure coding practices
- Continuous Monitoring: Real-time threat detection using SIEM and SOAR platforms
- Zero Trust Architecture: Never trust, always verify principle for all access requests
🧱 Question 2 8+4 Marks
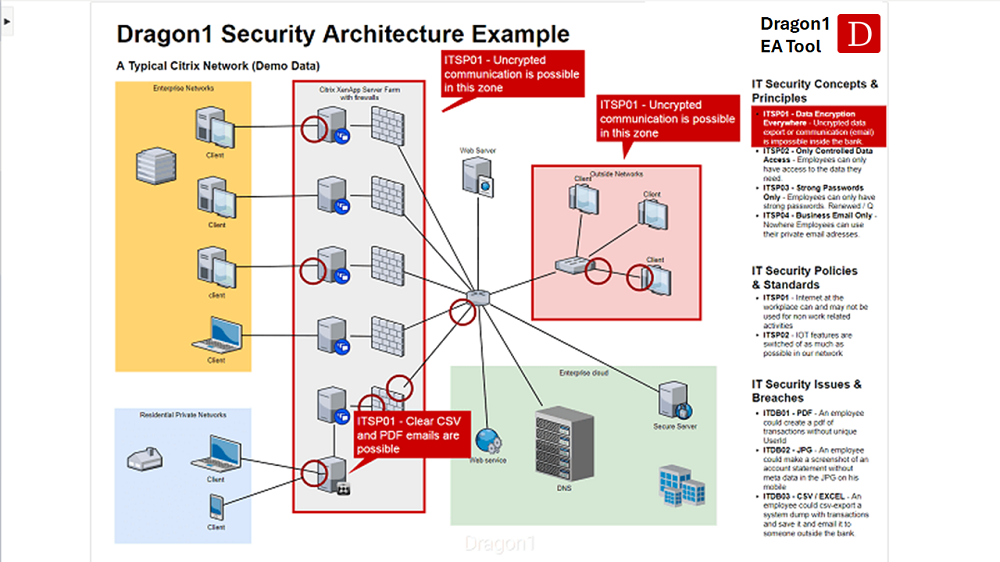
🧱 Benefits of Firewalls as Defense Mechanism

1. Network Perimeter Protection:
Firewalls act as the first line of defense, creating a barrier between trusted internal networks and untrusted external networks (Internet). They monitor and control incoming and outgoing traffic based on predetermined security rules.
2. Access Control:
Granular control over network traffic through rule-based filtering including IP addresses, port numbers, protocols, and application-level inspection.
3. Threat Prevention:
- Blocks unauthorized access attempts and port scanning
- Prevents malware from communicating with command & control servers
- Stops certain types of DoS attacks through rate limiting
- Filters malicious content and known attack signatures
4. Logging and Monitoring:
Comprehensive logging capabilities enable security teams to analyze traffic patterns, detect anomalies, and conduct forensic investigations.
5. VPN Support:
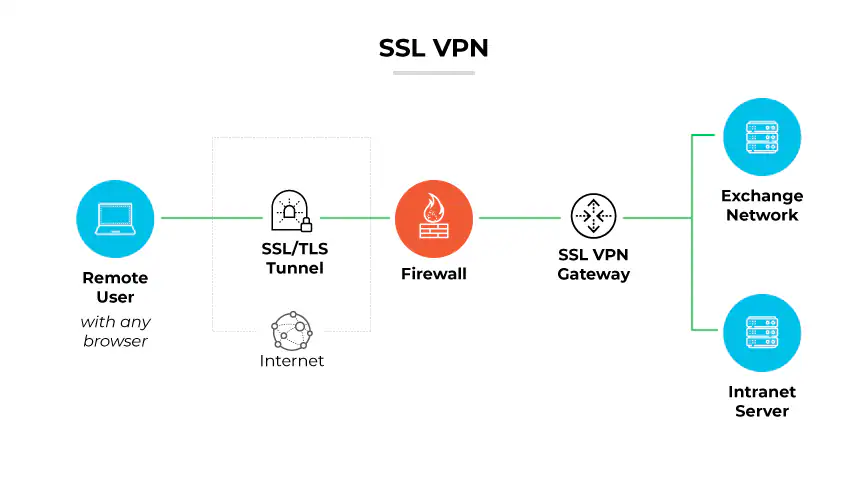
Modern firewalls provide secure remote access through VPN termination, encrypting traffic between remote users and corporate networks.
6. Application Awareness:
Next-Generation Firewalls (NGFW) can identify and control applications regardless of port or protocol used, enabling fine-grained policy enforcement.
🧱 Limitations of Firewalls
- Internal Threats: Cannot protect against insider threats or malware already inside the network
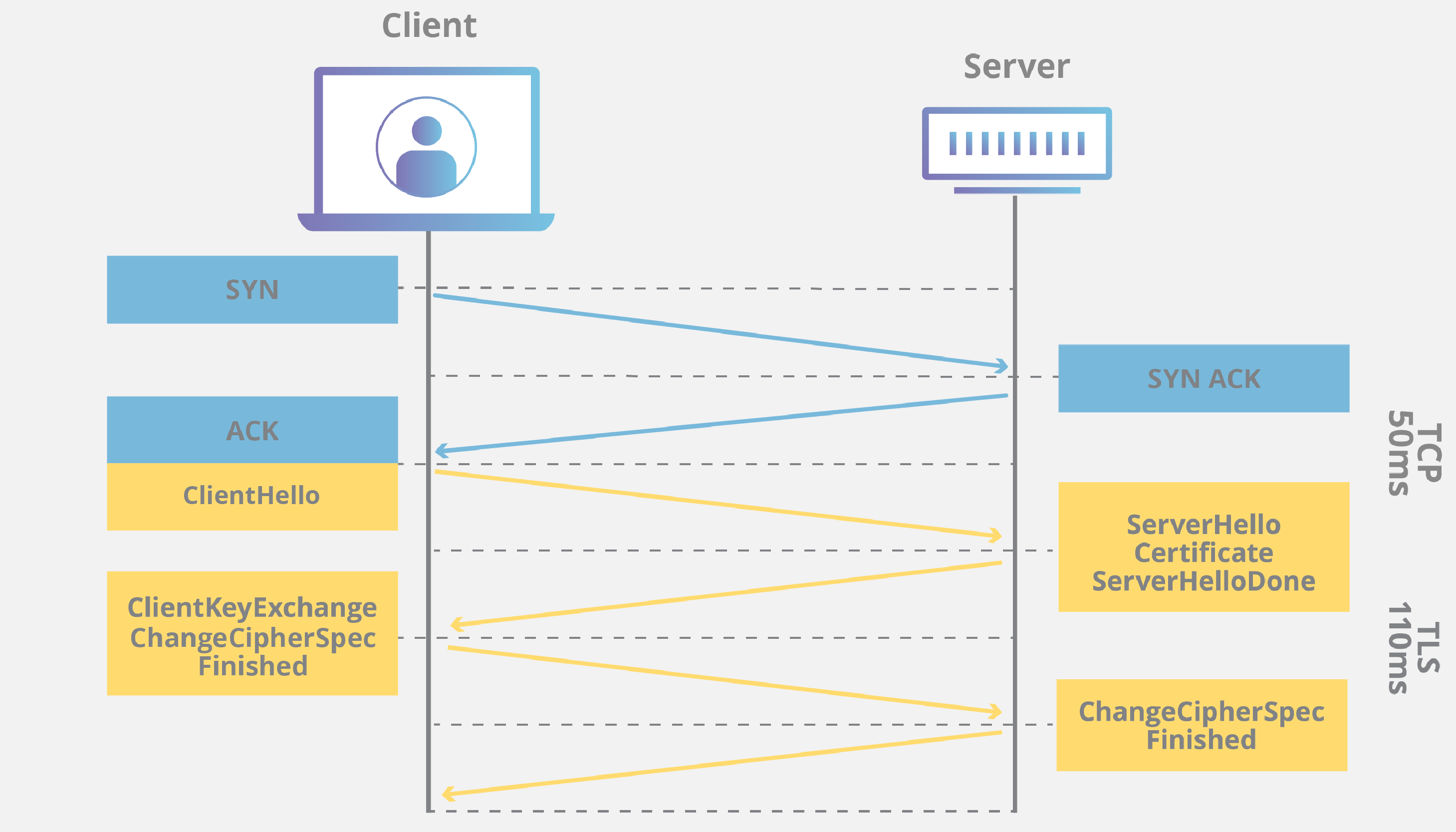
- Encrypted Traffic: Difficulty inspecting encrypted traffic (TLS/SSL) without SSL inspection capabilities
- Zero-Day Attacks: Signature-based detection fails against unknown threats
- Social Engineering: No protection against phishing or human manipulation
- Complexity: Misconfiguration can create security gaps; rule management becomes complex
- Performance Impact: Deep packet inspection can introduce latency
- Bypass Techniques: Tunneling, VPNs, and encrypted proxies can circumvent firewall controls
🧱 Features to Consider When Selecting a Firewall
| Feature Category | Specific Considerations |
|---|---|
| Performance | Throughput capacity (Gbps), concurrent connections, new connections per second, latency impact |
| Security Capabilities | IPS/IDS integration, malware sandboxing, URL filtering, SSL/TLS inspection, sandboxing |
| Scalability | Support for growth, cloud integration, virtual firewall options, clustering capabilities |
| Management | Centralized management, intuitive GUI, API availability, policy optimization tools |
| Integration | SIEM compatibility, threat intelligence feeds, SD-WAN integration, zero trust architecture support |
| Compliance | Logging standards, reporting capabilities, regulatory compliance features (PCI DSS, HIPAA) |
| Cost | TCO including licensing, support, hardware, training; subscription models vs perpetual licensing |
📋 Question 3 6+6 Marks
(b) Discuss about technical and non-technical aspects of security implementation.
(a) Employment Policies and Practices for Information Security
1. Pre-Employment Phase:
- Background Verification: Criminal record checks, employment history verification, education credential validation
- Security Clearance: For sensitive positions, appropriate clearance levels based on data access requirements
- NDA Agreements: Non-disclosure agreements protecting proprietary information
- Acceptable Use Policy (AUP) Review: Candidates must acknowledge IT resource usage policies before hiring
2. During Employment:
- Role-Based Access Control (RBAC): Principle of least privilege - employees access only necessary resources
- Security Awareness Training: Mandatory annual training covering phishing, social engineering, password hygiene
- Clear Desk Policy: Requirements for securing physical documents and devices
- Remote Work Policies: VPN usage, secure Wi-Fi requirements, device encryption standards
- Incident Reporting: Procedures for reporting suspicious activities or security breaches
- Regular Access Reviews: Quarterly reviews of user privileges and access rights
3. Termination/Transfer Procedures:
- Immediate Access Revocation: Timely disabling of accounts, VPN access, and building access
- Asset Return: Collection of laptops, mobile devices, access cards, and confidential materials
- Exit Interviews: Reminders of ongoing confidentiality obligations
- Knowledge Transfer: Secure handover of data and system access to replacements
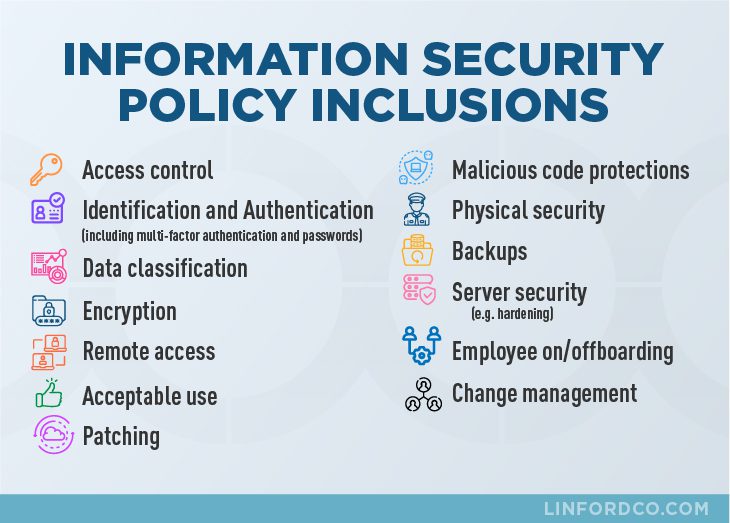
(b) Technical and Non-Technical Aspects of Security Implementation
Technical Aspects:
- Access Control Mechanisms: Multi-factor authentication (MFA), biometric systems, smart cards, password policies
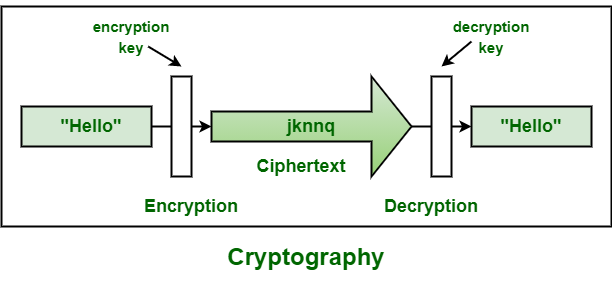
- Encryption: Data at rest (AES-256), data in transit (TLS 1.3), end-to-end encryption for communications
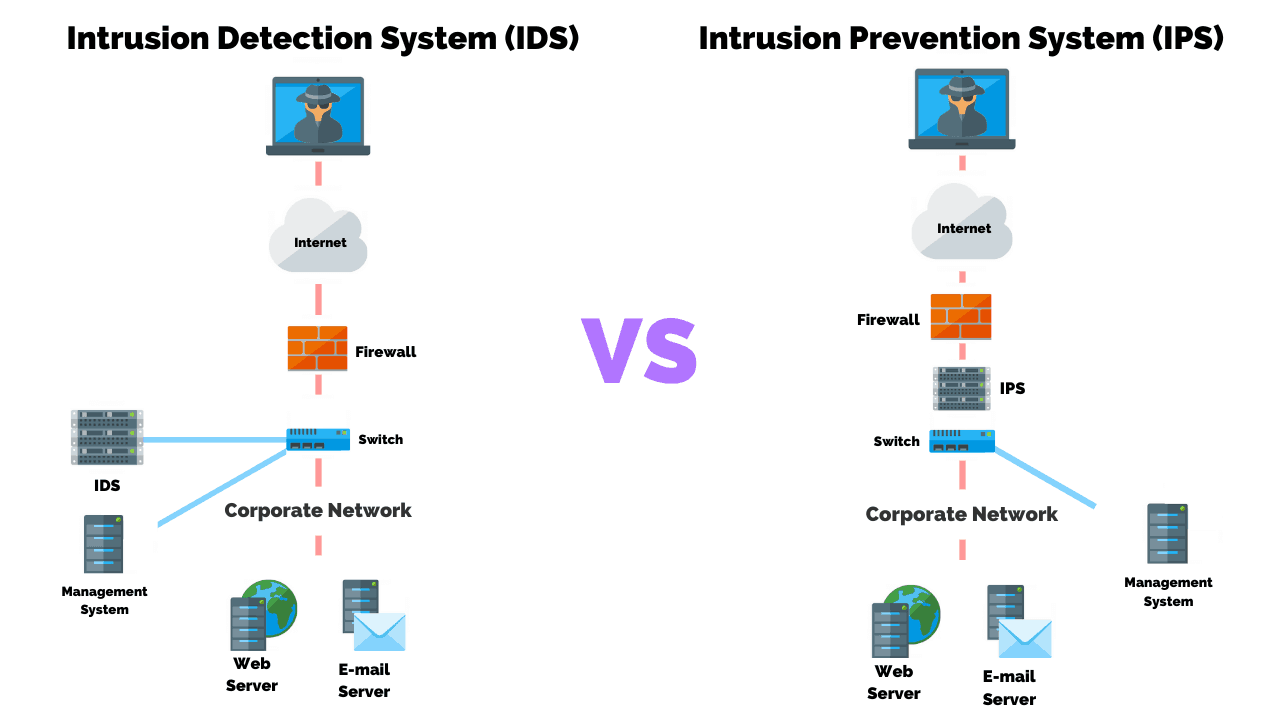
- Network Security: Firewalls, IDS/IPS, network segmentation, VLANs, VPNs
- Endpoint Protection: Antivirus/EDR, host-based firewalls, device encryption, patch management
- Security Monitoring: SIEM systems, log management, behavioral analytics, threat hunting
- Backup and Recovery: Automated backups, disaster recovery sites, business continuity planning
- Cloud Security: CASB (Cloud Access Security Broker), CSPM (Cloud Security Posture Management)
Non-Technical Aspects:
- Governance and Policies: Information security policies, standards, procedures, and guidelines aligned with business objectives
- Organizational Structure: Defined security roles (CISO, security officers), clear accountability and reporting lines
- Human Resources: Security awareness programs, background checks, disciplinary procedures for violations
- Physical Security: Facility access controls, surveillance systems, environmental controls (fire suppression, HVAC)
- Legal and Compliance: Regulatory adherence (GDPR, HIPAA, PCI-DSS), contract management, intellectual property protection
- Risk Management: Risk assessment methodologies, risk treatment plans, business impact analysis
- Third-Party Management: Vendor risk assessments, security requirements in contracts, supply chain security
- Incident Response: Communication plans, crisis management, public relations strategies
- Security Culture: Executive sponsorship, security champions program, reward systems for security-conscious behavior